Executive Summary
Between March 10 and March 19, 2026, a CrimsonVector analyst received three smishing text messages — two impersonating the Tennessee Department of Motor Vehicles / Department of Safety and Homeland Security, and one impersonating the Massachusetts Registry of Motor Vehicles. Despite targeting different states through different delivery channels and TLDs, the specimens share common infrastructure DNA while revealing real-time template evolution: the third specimen, arriving just nine days after the first, shows the operators correcting previously documented tells — fixing the agency name, dropping fabricated statutes, and shifting from aggressive threats to measured bureaucratic language.
Analysis of both specimens' indicators maps them directly to the Lighthouse phishing kit, a Phishing-as-a-Service (PhaaS) platform operated by a China-based cybercrime syndicate tracked as the Smishing Triad (PRODAFT designation: LARVA-241). The Lighthouse kit has powered one of the most expansive smishing campaigns in U.S. history, with over 194,000 malicious domains, an estimated $1 billion in illicit revenue over three years, and an estimated 12.7 to 115 million stolen payment cards in the United States alone.
This article documents all three specimens, traces them through the campaign's known infrastructure and tradecraft, and assesses the operational status of the Smishing Triad following Google's November 2025 RICO lawsuit and the brief disruption of Lighthouse infrastructure. The receipt of these specimens in March 2026 — targeting two different states with different TLDs, sender infrastructure, delivery protocols, and evolving social engineering language — confirms the campaign has not only reconstituted but is actively diversifying its operational footprint and refining its lure quality in response to public exposure.
The Specimens
Specimen A — Tennessee DMV (March 10, 2026)
At 10:15 AM EST on March 10, 2026, a text message was received via iMessage from the number +63 951 531 0714 (Philippines country code). The message body read:
Tennessee DMV Final Notice
Penalties Start March 11
Our records show an unpaid traffic ticket. By order of Tennessee Code 15C-16.003, payment due March 10, 2026.
1. Report violation to DMV database
2. Suspend registration starting March 11
3. 30-day suspension of driving privileges
4. Collection agency + 35% service fee
5. Legal action and credit score impact
Pay Now: https://tn.org-htmct[.]bond/dmv
Act now to prevent license suspension.
(Reply Y to use link or copy to browser.)
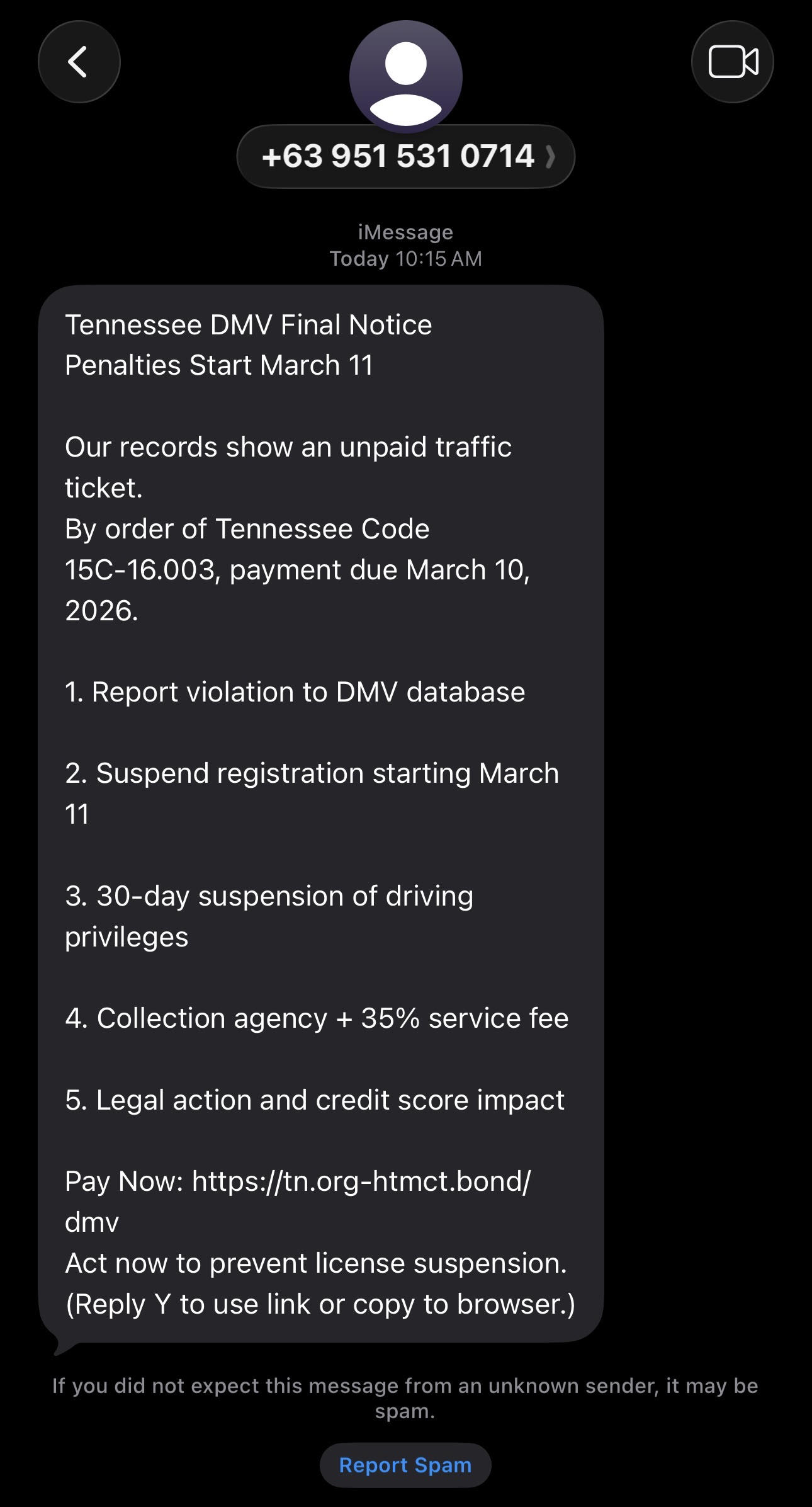
The recipient's device flagged the message with "If you did not expect this message from an unknown sender, it may be spam" and offered a Report Spam option — Apple's standard iMessage filtering for unknown senders.
Specimen B — Massachusetts RMV (March 17, 2026)
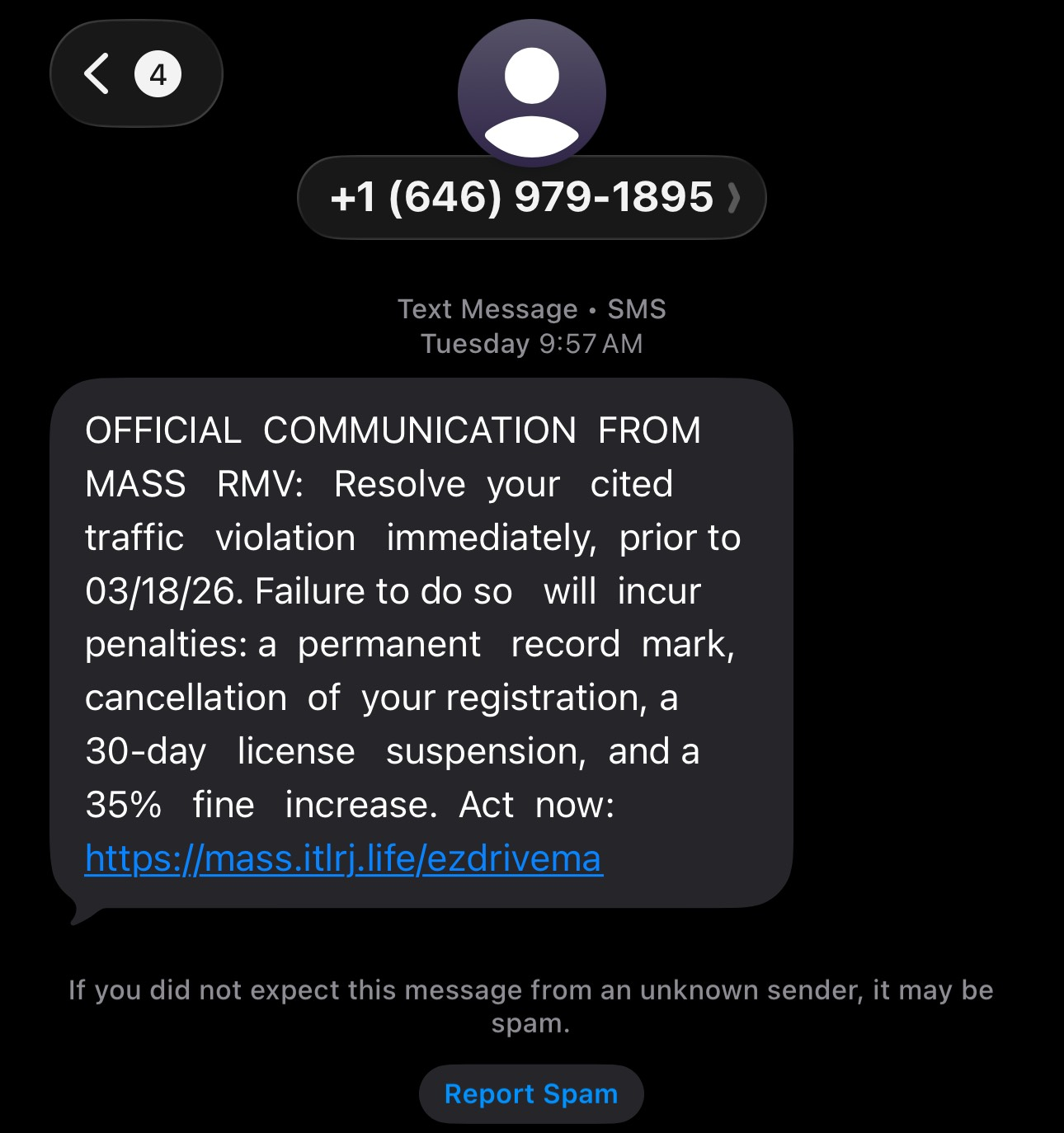
One week later, at 9:57 AM EST on March 17, 2026, a second text message was received — this time via SMS (green bubble, not iMessage) from the number +1 (646) 979-1895 (New York City area code). The message body read:
OFFICIAL COMMUNICATION FROM MASS RMV: Resolve your cited traffic violation immediately, prior to 03/18/26. Failure to do so will incur penalties: a permanent record mark, cancellation of your registration, a 30-day license suspension, and a 35% fine increase. Act now: https://mass.itlrj[.]life/ezdrivema
This specimen also triggered Apple's unknown-sender warning and Report Spam option.
Specimen C — Tennessee TDOSHS (March 19, 2026)
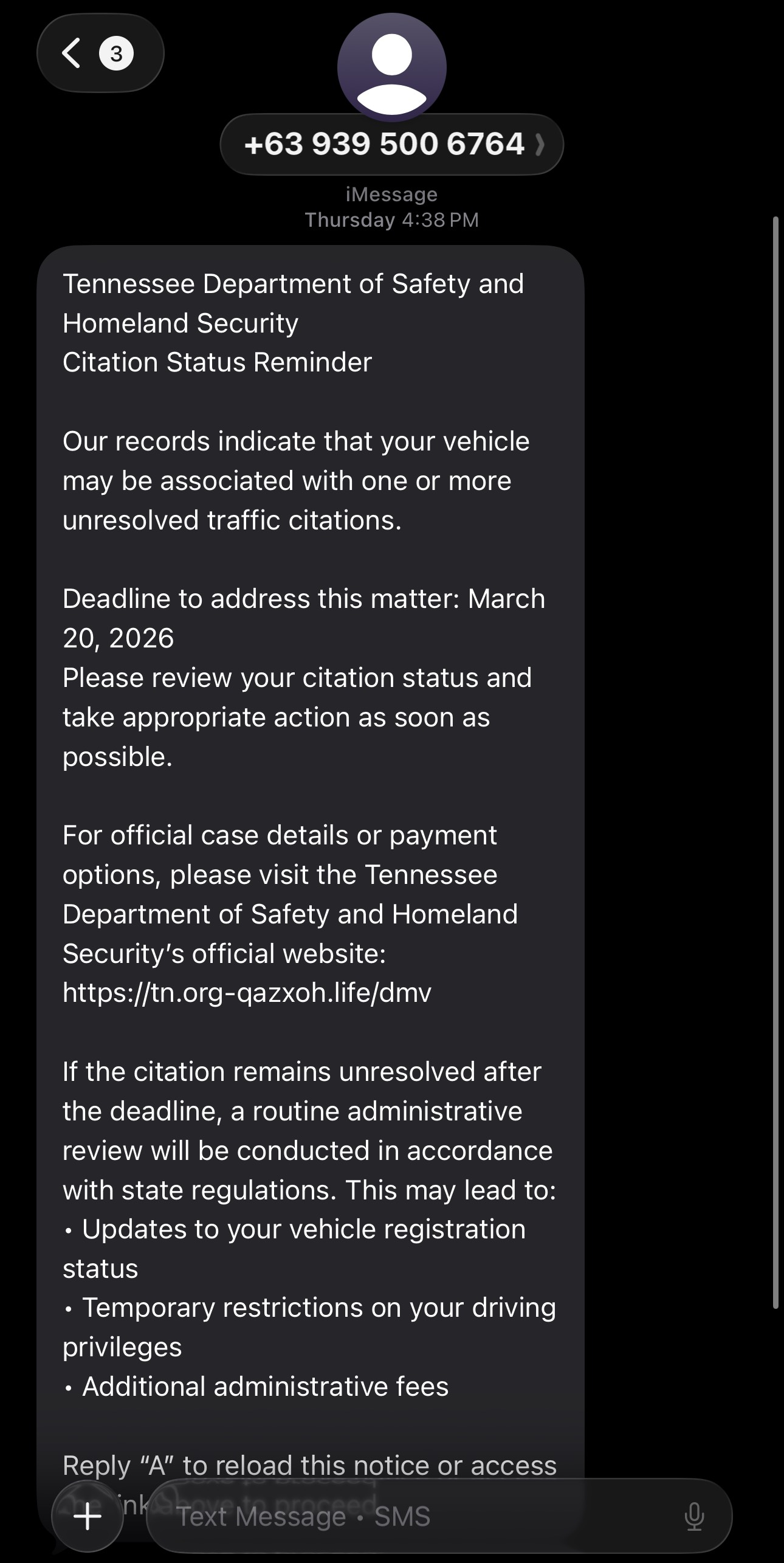
Nine days after the first specimen, at 4:38 PM EST on March 19, 2026, a third text message was received via iMessage from +63 939 500 6764 (Philippines). This specimen represents a significant template evolution:
Tennessee Department of Safety and Homeland Security
Citation Status Reminder
Our records indicate that your vehicle may be associated with one or more unresolved traffic citations.
Deadline to address this matter: March 20, 2026
Please review your citation status and take appropriate action as soon as possible.
For official case details or payment options, please visit the Tennessee Department of Safety and Homeland Security's official website: https://tn.org-qazxoh[.]life/dmv
If the citation remains unresolved after the deadline, a routine administrative review will be conducted in accordance with state regulations. This may lead to:
• Updates to your vehicle registration status
• Temporary restrictions on your driving privileges
• Additional administrative fees
Reply "A" to reload this notice or access the link above to proceed.
This specimen also triggered Apple's unknown-sender warning and Report Spam option.
Comparative Analysis
The three specimens, received across a nine-day window, reveal both the campaign's breadth and its real-time evolution:
| Attribute | Specimen A (TN) | Specimen B (MA) | Specimen C (TN) |
| Date | March 10, 2026 | March 17, 2026 | March 19, 2026 |
| Impersonated Entity | Tennessee DMV | Massachusetts RMV | TN Dept. of Safety & Homeland Security |
| Sender | +63 (Philippines) | +1 646 (NYC) | +63 (Philippines) |
| Delivery Protocol | iMessage | SMS | iMessage |
| Payload Domain | tn.org-htmct[.]bond/dmv | mass.itlrj[.]life/ezdrivema | tn.org-qazxoh[.]life/dmv |
| Root Domain | htmct[.]bond | itlrj[.]life | qazxoh[.]life |
| TLD | .bond | .life | .life |
| Fabricated Statute | "Tennessee Code 15C-16.003" | None | None |
| Penalty Specificity | Explicit (30-day, 35%) | Explicit (30-day, 35%) | Vague ("temporary," "additional") |
| Tone | Aggressive/threatening | Directive/urgent | Bureaucratic/professional |
| Reply Mechanism | "Reply Y" | None | "Reply A" |
| Agency Name Accuracy | Incorrect ("DMV") | Correct ("MASS RMV") | Correct (full TDOSHS name) |
| Deadline Pressure | Same-day | Next-day | Next-day |
Template evolution in real time. The progression from Specimen A to Specimen C — both targeting Tennessee, just nine days apart — is the most analytically significant finding in this investigation. Specimen A used the generic "Tennessee DMV," a fabricated statute, aggressive five-point penalties with specific numbers, and "Reply Y." Specimen C uses the correct agency name (Tennessee Department of Safety and Homeland Security), drops the fabricated statute entirely, replaces specific penalty numbers with vague bureaucratic language ("temporary restrictions," "additional administrative fees"), and rotates the reply letter to "A." The tone shifts from threatening to the kind of measured, procedural language a real government agency might use. This is iterative refinement of a social engineering template, likely informed by public reporting of the campaign's earlier tells.
Infrastructure constants persist. Despite the template overhaul, the underlying domain architecture is unchanged. Specimen C's tn.org-qazxoh[.]life/dmv follows the exact same pattern as Specimen A's tn.org-htmct[.]bond/dmv: the format tn.org-[random string].[TLD]/dmv with a Philippine +63 sender over iMessage. The skeleton is identical — only the skin has been upgraded.
TLD convergence on .life. Specimens B and C both use .life, while only Specimen A used .bond. This may indicate the campaign is consolidating on .life as its current preferred TLD, potentially because .bond has already been flagged in blocklists following abuse documentation.
Specimen B introduces a hybrid lure: the message body impersonates the Massachusetts RMV for a traffic violation, but the URL path /ezdrivema references EZDriveMA, the state's electronic toll collection system. This blends two separate Massachusetts-specific brands into a single message — a sloppy crossover that suggests the kit is drawing from a template library where toll and DMV lures share infrastructure.
Initial Triage: Red Flags at a Glance
All three specimens present high-confidence indicators of a smishing campaign, though Specimen C's refined language makes it the most convincing of the set. Specimen A is analyzed in detail below; Specimens B and C share most patterns with the variations noted in the comparative table above.
Sender origin. Specimen A's +63 country code belongs to the Philippines. No U.S. state agency would originate communications from a foreign mobile number. Specimen B uses a domestic 646 (NYC) number — a shift toward harder-to-filter sender infrastructure, though still anomalous for a Massachusetts state agency. Tennessee state government communications use @tn.gov email addresses, and the Department of Safety and Homeland Security has publicly confirmed it does not send text messages about overdue fines, fees, or license status. Likewise, Massachusetts RMV Registrar Colleen Ogilvie has publicly stated that "the Massachusetts Registry of Motor Vehicles never asks for payment via a text link."
Fabricated statute. The message cites "Tennessee Code 15C-16.003." Tennessee Code Annotated follows a Title-Chapter-Part-Section format (e.g., T.C.A. § 55-50-502 for license suspension). The cited code does not exist. As we will see, this exact citation format is a known fingerprint of the Lighthouse phishing kit.
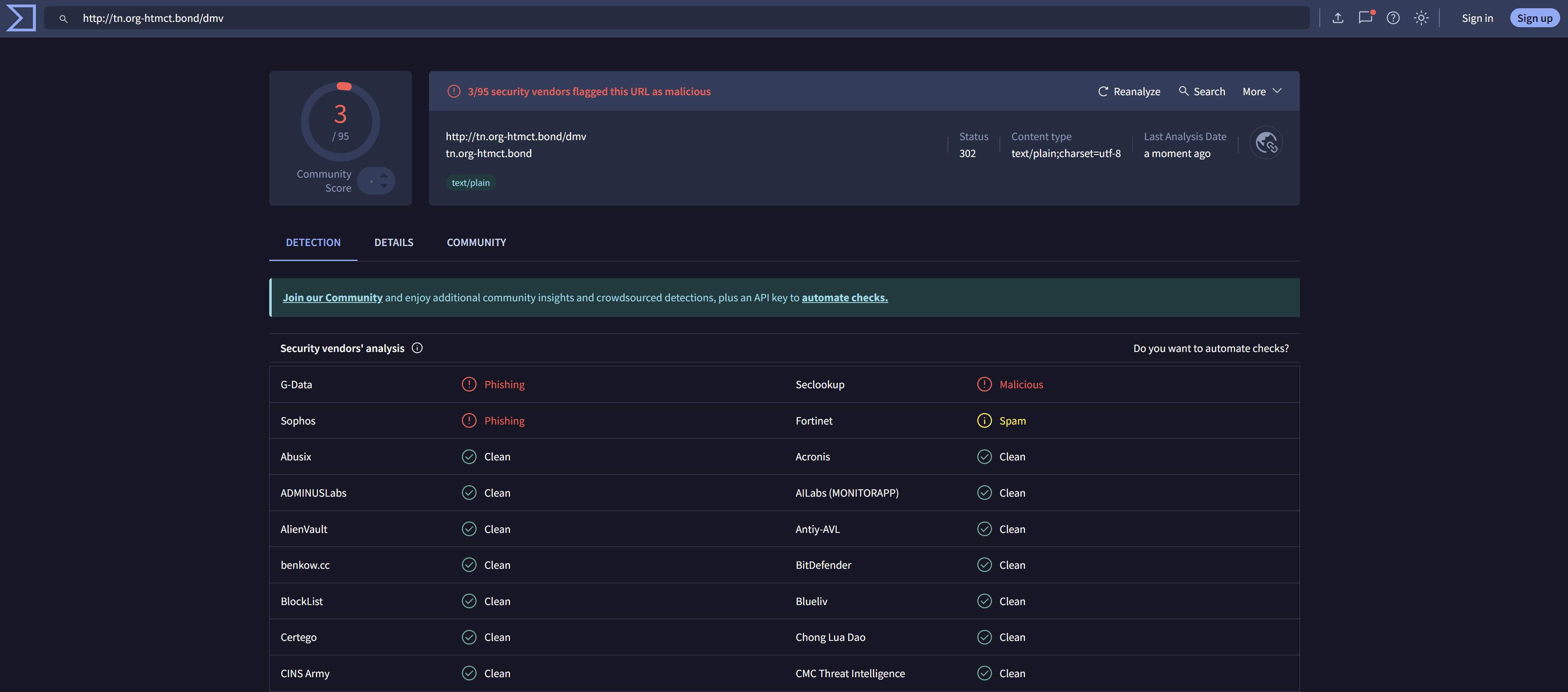
Hostile domain architecture. Specimen A's payment URL tn.org-htmct[.]bond/dmv exploits visual parsing — the subdomain prefix tn.org- suggests a connection to Tennessee or a .org domain, but the actual registered domain is htmct[.]bond, a randomly generated string on the .bond TLD. Specimen B's mass.itlrj[.]life/ezdrivema follows the same pattern: mass. as a subdomain prefix for Massachusetts, with the real domain being itlrj[.]life — another random string, this time on the .life TLD. Neither .bond nor .life are associated with any government entity. Official Tennessee government websites operate under .gov; Massachusetts uses .mass.gov.
![Phishing landing page at tn.org-htmct[.]bond/dmv](02_landing_page.png)
Urgency escalation cascade. The five-point penalty structure — escalating from a database report to registration suspension, license suspension, collections with a 35% fee, and finally legal action with credit impact — follows a classic social engineering pressure model designed to override critical thinking through fear of compounding consequences.
Same-day deadline. The message claims payment is due March 10, 2026 — the same day it was received — with penalties beginning March 11. This compressed timeline is a hallmark of smishing campaigns, designed to prevent recipients from independently verifying the claim.
"Reply Y" engagement technique. This is a known mechanism to bypass Apple iMessage's link protection. iMessage automatically disables clickable links in messages from unknown senders. By prompting the recipient to reply, the attacker establishes a two-way conversation, which re-enables the links for interaction in subsequent messages. It also confirms the number is live and actively monitored, making it more valuable for future targeting.
Campaign Attribution: The Lighthouse Phishing Kit
The Fabricated Statute — A Signature Fingerprint
The citation "Tennessee Code 15C-16.003" is not an isolated fabrication. In June 2025, Check Point Research published a detailed analysis of a DMV-themed phishing campaign impersonating multiple U.S. state DMVs, noting that the scam messages routinely cited fictitious legal codes following the exact pattern "[State-Name] Administrative Code 15C-16.003." This identical template has been documented across Tennessee, Nebraska, Colorado, New York, New Jersey, California, Florida, Texas, and other states — with only the state name and payment deadline swapped per target.
Earlier documented Tennessee specimens from June 2025 cited "North Tennessee State Administrative Code 15C-16.003" — a doubly fabricated reference, since "North Tennessee" does not exist as a jurisdictional entity. Specimen A (March 10) shows a first-pass refinement: the template has been updated to the more plausible "Tennessee Code," suggesting iterative improvement of the lure language. But Specimen C (March 19) goes further — it drops the fabricated statute entirely. This is a significant operational indicator: public reporting of the "15C-16.003" pattern as a campaign fingerprint (including by Check Point, WKRN, and multiple law enforcement agencies) appears to have driven the operators to remove it altogether. The fabricated statute is becoming a burned indicator — still useful for detecting earlier variants, but no longer reliable as a sole detection signal for current-generation templates.
Sender Infrastructure: Philippine Origin
Check Point's analysis confirmed that the SMS messages in this campaign were primarily sent from spoofed numbers traced to origins in the Philippines. The +63 country code on the March 2026 specimen is consistent with this documented delivery infrastructure. The Smishing Triad's operational model leverages SMS gateways and spoofing techniques to send messages at scale — thousands per hour, according to FBI Supervisory Special Agent David Palmer, who described the operation as run by organized criminal groups overseas using technology and AI for mass message delivery.
Domain Analysis: TLD Rotation to .bond and .life
The earlier wave of the campaign, documented extensively by Check Point, Palo Alto Networks Unit 42, and Silent Push, relied heavily on .cfd and .win TLDs, following the pattern https://[state_ID]dmv.gov-[4-letter-string].cfd/pay. These TLDs were chosen for their low registration cost and minimal verification requirements. EZDriveMA-specific spoofing domains used .top and .xin patterns, such as ezdrivema.com-payzk.top and ezdrivema.com-woleww.xin.
The March 2026 specimens use two new TLDs — .bond and .life — neither of which appear in the earlier documented campaigns. The .bond extension, managed by ShortDot SA and available since 2019, has become heavily associated with cybercriminal abuse. Research by Infoblox documented the "Revolver Rabbit" cybercriminal gang registering over 500,000 domains on .bond alone for malware distribution, and Spamhaus has consistently ranked .bond among the TLDs with the highest rates of malware association.
The domain structure also shows evolution. Where earlier specimens used a pattern like nydmv.gov-abcd[.]cfd/pay (embedding a state identifier and .gov string in the subdomain), the March 2026 specimens use simpler subdomain prefixes — tn.org- and mass. — potentially to evade pattern-based detection rules written against the earlier dmv.gov- format.
Specimen B's /ezdrivema URL path is particularly notable. EZDriveMA is Massachusetts' electronic toll collection system — a completely separate entity from the RMV. The message body claims to be about a traffic violation (an RMV matter), but the URL references the toll system. This hybrid construction suggests the kit is drawing from a shared template library where toll scam and DMV/RMV lure components are mixed, possibly by operators who lack familiarity with the distinctions between U.S. state agencies. Previous EZDriveMA smishing campaigns, documented by MassDOT as early as June 2024, also used Philippine +63 sender numbers — though Specimen B has shifted to a domestic NYC number.
![Silent Push infrastructure analysis for tn.org-htmct[.]bond](06_silentpush.png)
![URLScan.io result for tn.org-htmct[.]bond](04_urlscan_result.png)
The Smishing Triad: Threat Actor Profile
Identity and Attribution
The Lighthouse phishing kit is the operational product of a China-based cybercrime syndicate tracked under multiple designations:
| Designation | Source |
| Smishing Triad | Resecurity, Silent Push, Check Point |
| LARVA-241 | PRODAFT |
| Wang Duo Yu / Lao Wang | Individual developer attribution |
The kit's developer, tracked as Wang Duo Yu, has been described as a computer science student in China who monetized his technical skills through PhaaS development. He sold access to the Lighthouse kit on Telegram channels, with pricing ranging from $50 for full-feature deployments to $20 for version updates and miscellaneous support.
The Smishing Triad operates not as a single monolithic group, but as a phishing-as-a-service ecosystem — a supply chain of specialized criminal actors including data brokers, domain sellers, hosting providers, phishing kit developers, SMS and RCS spammers, and blocklist evasion specialists. Silent Push reported the group boasted "300+ front desk staff worldwide" supporting kit operations.
Scale of Operations
The numbers behind the Smishing Triad are staggering:
- 194,000+ malicious domains registered since January 2024 (Palo Alto Networks Unit 42)
- ~25,000 domains live at any given time during an 8-day period (Silent Push)
- $1 billion+ in estimated illicit revenue over three years (Wall Street Journal)
- 12.7 to 115 million payment cards estimated stolen in the U.S. alone (Google lawsuit filing)
- 200,000 fraudulent websites created using Lighthouse in a single 20-day period (Google)
- 120+ countries targeted globally
- 600+ phishing templates impersonating 400+ entities
The kit targeted an extraordinarily broad range of sectors: postal and logistics services, telecommunications, transportation and toll systems, financial institutions, retail, government agencies, and public services. The DMV impersonation campaign represents just one operational vertical within a much larger enterprise.
Technical Infrastructure
Check Point's forensic analysis of the campaign revealed a highly structured technical footprint:
DNS infrastructure. All associated phishing domains in the documented campaign used Alibaba's DNS services (alidns.com / dns8.alidns.com), with SOA contact addresses pointing to hostmaster@hichina.com — a strong attribution link to Chinese domain operations.
Web asset fingerprinting. DOM analysis revealed each phishing site included a static set of five reused files: two JavaScript files (C18UmYZN.js, fliceXIj.js), one CSS file (C0Zfn5GX.css), and two image assets (BHcjXi3x.gif, BkBiYrmZ.svg). This reuse across thousands of domains confirmed a centralized phishing kit model.
Source code attribution. Chinese-language comments were found embedded in the phishing site source code, reinforcing attribution to Chinese-speaking developers.
Hosting concentration. Over 50% of DNS query volume for Smishing Triad domains was served from U.S.-based infrastructure, particularly Cloudflare (AS13335), while domain registration concentrated in China through Hong Kong-based registrar Dominet (HK) Limited. This hybrid model — Chinese registration with U.S. hosting — provides both resilience and the performance benefits of major cloud providers.
The Tennessee Context
Tennessee has been a particularly notable target in this campaign's evolution. FBI Supervisory Special Agent David Palmer, who supervises white-collar crime investigations in West Tennessee, provided crucial context in a June 2025 interview: the DMV smishing wave is a direct successor to the toll road scam that swept the country earlier. As Palmer noted, the toll scam struggled in Tennessee because the state has no toll roads, so the criminal organizations adapted — pivoting from tolls to DMV impersonation.
The Tennessee Department of Safety and Homeland Security (TDOSHS) and the Tennessee Highway Patrol both issued formal warnings, confirming that TDOSHS does not send text messages about overdue traffic fines, fees, payments, or license status. Multiple local agencies — Clarksville Police Department, Kingsport Police Department, Johnson City Police Department, and the Washington County Sheriff's Office — also issued public alerts.
The refinement visible across our March 2026 specimens documents three generations of Tennessee-targeting templates. The June 2025 wave used "North Tennessee State Administrative Code 15C-16.003" and "Tennessee Department of Vehicles" — both containing easy-to-spot errors. Specimen A (March 10) corrected the agency reference to "Tennessee DMV" and simplified the statute to "Tennessee Code 15C-16.003" — still fabricated, but more plausible. Specimen C (March 19) represents a generational leap: the correct full agency name, no fabricated statute, professional bureaucratic tone, and hedging language ("may be associated," "may lead to"). This three-stage progression — visible across just nine months of documented activity — demonstrates the speed at which PhaaS template quality is improving. As Massachusetts RMV Registrar Colleen Ogilvie warned at a state budget hearing just days before Specimen C was sent: "With the advance of AI technology and advanced technologies, these bad actors can adjust these messages really quickly to make them really look like state-issued messages."
Post-Disruption Resurgence
The Google Lawsuit (November 2025)
On November 12, 2025, Google filed a landmark civil lawsuit in the U.S. District Court for the Southern District of New York against 25 unnamed individuals under the Racketeer Influenced and Corrupt Organizations (RICO) Act, the Lanham Act, and the Computer Fraud and Abuse Act (CFAA). Google described Lighthouse as a "phishing for dummies" tool and detailed its role in powering massive volumes of smishing attacks globally.
Within days, Lighthouse operations appeared to be disrupted. The threat actors posted a Chinese-language message on Telegram stating their "cloud server has been blocked due to malicious complaints." Silent Push confirmed that all previously tracked Lighthouse Telegram channels were deleted or taken down for Telegram Terms of Service violations.
Signs of Reconstitution
However, the disruption was incomplete. Silent Push noted at the time that many websites were still active using Lighthouse kit code, and other Smishing Triad-associated phishing kits remained operational. The broader PhaaS ecosystem — including related platforms like Darcula and Lucid — continued to function.
The March 2026 specimens received by CrimsonVector confirm that the campaign has resumed active operations against multiple U.S. states simultaneously, with notable tactical adjustments:
TLD rotation — shifting from
.cfdand.winto.bondand.life, with apparent convergence on.life(used in two of three specimens), likely to evade domain-level blocking rules implemented after the earlier wavesAggressive template refinement — Specimen C (March 19) corrects the agency name to "Tennessee Department of Safety and Homeland Security," drops the fabricated statute fingerprint, and adopts professional bureaucratic language — all within nine days of Specimen A's more primitive variant hitting the same target state
Diversified sender infrastructure — using both Philippine international numbers (Specimens A, C) and domestic U.S. numbers with major metro area codes (Specimen B, 646/NYC)
Protocol diversification — deploying via both iMessage (Specimens A, C) and SMS (Specimen B), maximizing coverage across Apple's messaging ecosystem
Hybrid lure construction — blending RMV and EZDriveMA brands in Specimen B, suggesting operators are mixing template components from the kit's toll and motor vehicle libraries
Reply mechanism rotation — shifting from "Reply Y" (Specimen A) to "Reply A" (Specimen C), likely to evade carrier-level content filtering tuned to the earlier pattern
Indicator burndown — the removal of the "15C-16.003" statute and the correction of agency names suggest the operators are actively monitoring public reporting and security research about their campaign
This pattern is consistent with the Smishing Triad's documented operational resilience. Unit 42 found that 83% of the group's domains were active for less than two weeks, with 29% lasting only two days — a domain churning strategy specifically designed to outpace blocklists and takedowns. The shift to .bond TLDs represents a continuation of this approach at the TLD level itself.
Indicators of Compromise (IOCs)
Specimen A — Tennessee DMV (March 10, 2026)
| Sender | +63 951 531 0714 (Phone Number) |
| Sender Country | Philippines (+63) (Origin) |
| Payload URL | tn.org-htmct[.]bond/dmv (Domain) |
| Root Domain | htmct[.]bond (Domain) |
| TLD | .bond (Infrastructure) |
| Fabricated Statute | "Tennessee Code 15C-16.003" (Lure Element) |
| Delivery Vector | iMessage (SMS/RCS) (Method) |
Specimen B — Massachusetts RMV (March 17, 2026)
| Sender | +1 (646) 979-1895 (Phone Number) |
| Sender Area Code | New York City (646) (Origin) |
| Payload URL | mass.itlrj[.]life/ezdrivema (Domain) |
| Root Domain | itlrj[.]life (Domain) |
| TLD | .life (Infrastructure) |
| Spoofed Brand | EZDriveMA (MA toll system) (Lure Element) |
| Delivery Vector | SMS (Method) |
Specimen C — Tennessee TDOSHS (March 19, 2026)
| Sender | +63 939 500 6764 (Phone Number) |
| Sender Country | Philippines (+63) (Origin) |
| Payload URL | tn.org-qazxoh[.]life/dmv (Domain) |
| Root Domain | qazxoh[.]life (Domain) |
| TLD | .life (Infrastructure) |
| Impersonated Agency | TN Dept. of Safety & Homeland Security (Lure Element) |
| Reply Mechanism | "Reply A" (Engagement) |
| Delivery Vector | iMessage (Method) |
| Known Malicious IP | 49.51.75[.]162 (Infrastructure) |
| DNS Provider | alidns.com / dns8.alidns.com (Infrastructure) |
| SOA Contact | hostmaster@hichina[.]com (Attribution) |
| Domain Pattern | [state_ID]dmv.gov-[string].[TLD]/pay (Infrastructure) |
| JS Asset | C18UmYZN.js (Kit Fingerprint) |
| JS Asset | fliceXIj.js (Kit Fingerprint) |
| CSS Asset | C0Zfn5GX.css (Kit Fingerprint) |
| Image Asset | BHcjXi3x.gif (Kit Fingerprint) |
| Image Asset | BkBiYrmZ.svg (Kit Fingerprint) |
| NJ | 288f3cb007f3ad99835a541b6be7e07f64aa7f7a56025518f02a1f0af41585b0 |
| CA | 5df0fcc2b6b3d3e52fb635c0b7bac41d27b5b75cbfeb16c024d66a59657d5535 |
| TX | 94126506523ebbf35ec9689f593d061453ab39395bf63098464dcbc270ee7f48 |
| FL | 2f71a0956b7f073735dab092b0fb8e4c222538cf0a6bbdf7517a02ece6934157 |
| GA | e88b894cc69c4f4ec5f6fdb2e7a0314601241571bf02154412c0168973fdc4df |
| PA | 5c7b246ec5b654c6ba0c86c89ba5cbaa61d68536efc32283da7694ed8e70b16d |
Defensive Recommendations
For Individuals
Never click links in unsolicited text messages about fines, tickets, or government actions. Navigate directly to official
.govwebsites by typing the URL into your browser.Verify the sender. Tennessee state government communications use
@tn.govemail addresses. The TDOSHS and THP do not send payment-related text messages.Do not reply to suspicious messages. Even replying "STOP" or "Y" confirms your number is active and monitored.
Report smishing messages. Forward suspicious texts to 7726 (SPAM), file complaints at reportfraud.ftc.gov, and report to the FBI's Internet Crime Complaint Center (IC3) at ic3.gov.
For Organizations and Security Teams
Block high-abuse TLDs at the DNS level, including
.bond,.life,.cfd,.win,.top,.xin,.vip,.world,.xyz, and.icu, or apply enhanced inspection to traffic destined for these TLDs.Implement IOC-based detection. Ingest the IOCs listed above into your SIEM, firewall, and DNS filtering platforms. Share indicators via MISP or other threat intelligence sharing platforms.
Monitor for the fabricated statute pattern — but don't rely on it. The string "15C-16.003" remains a high-fidelity indicator of earlier Lighthouse-kit variants. However, Specimen C demonstrates this indicator is being actively burned; current-generation templates may omit it entirely. Detection rules should also key on domain architecture patterns (
[state].org-[random].[TLD]/dmv) and the reply-to-activate engagement mechanism ("Reply Y," "Reply A," or similar).Deploy email authentication protocols — DMARC, SPF, and DKIM — to mitigate spoofed domain abuse in email-based variants of this campaign.
Educate users proactively. Share awareness materials about the DMV smishing campaign through internal communications, particularly for organizations with employees in targeted states.
Conclusion
The three specimens analyzed in this investigation are not isolated scam texts. They are nodes in one of the most extensive phishing-as-a-service operations ever documented — a China-based criminal ecosystem that has registered nearly 200,000 malicious domains, stolen tens of millions of payment cards, and generated over a billion dollars in illicit revenue across 120+ countries.
The Smishing Triad's pivot from toll scams to DMV/RMV impersonation demonstrates adversarial adaptation. The progression from Specimen A to Specimen C — both targeting Tennessee, nine days apart — demonstrates something more concerning: active template evolution informed by defensive reporting. The operators are reading the news. They corrected the agency name that law enforcement flagged. They dropped the fabricated statute that security researchers documented as a fingerprint. They softened the language that consumer advocates identified as a red flag. The next generation of this template will be harder to distinguish from a legitimate government communication by visual inspection alone.
The three specimens together paint a picture of an operation diversifying across every variable: state targets, sender infrastructure (Philippine vs. domestic U.S. numbers), delivery protocols (iMessage vs. SMS), TLDs (.bond, .life), lure construction, and social engineering tone. The persistent infrastructure pattern — [state].org-[random].[TLD]/dmv with Philippine sender numbers — remains the most reliable detection anchor, even as the message content evolves.
For residents of any U.S. state, the core message is straightforward: your state DMV, RMV, or Department of Motor Vehicles will never text you about unpaid tickets, and any message claiming otherwise is a scam — even if it sounds professional and cites the correct agency name. For the threat intelligence community, these specimens confirm the Smishing Triad's campaign remains active, operationally resilient against takedown efforts, and engaged in rapid iterative refinement that is actively burning previously documented indicators of compromise.
References
- Check Point Research. "DMV-Themed Phishing Campaign Targeting U.S. Citizens." Check Point Blog. June 17, 2025.
- Tennessee Department of Safety and Homeland Security. "Tennessee Department of Safety and Homeland Security and Tennessee Highway Patrol Warn of 'Outstanding Traffic Ticket' Scam." June 5, 2025.
- WREG News. "FBI investigates viral DMV text scam; unpaid ticket message is fake." June 11, 2025.
- Palo Alto Networks Unit 42. "The Smishing Deluge: China-Based Campaign Flooding Global Text Messages." November 20, 2025.
- Google. Lawsuit Filing, U.S. District Court, Southern District of New York. November 12, 2025.
- Dark Reading. "Google Looks to Dim 'Lighthouse' Phishing Kit." November 12, 2025.
- The Hacker News. "Google Sues China-Based Hackers Behind $1 Billion Lighthouse Phishing Platform." November 18, 2025.
- SecurityWeek. "Google Says Chinese 'Lighthouse' Phishing Kit Disrupted Following Lawsuit." November 14, 2025.
- CyberScoop. "Google, researchers see signs that Lighthouse text scammers disrupted after lawsuit." November 14, 2025.
- Silent Push. "Smishing Triad: Chinese eCrime Group Targets 121+ Countries, Intros New Banking Phishing Kit." May 15, 2025.
- The Hacker News. "Smishing Triad Linked to 194,000 Malicious Domains in Global Phishing Operation." October 24, 2025.
- WKRN News. "Middle TN authorities warn about traffic ticket scam texts." June 5, 2025.
- CircleID. "An Unnatural .Bond: A Study of a 'Megacluster' of Malware Domains." July 2024.
- Online Threat Alerts. "Nebraska DMV Text Scam." March 8, 2026.
CrimsonVector is the investigative research practice of Diego Parra. Defanged URLs and IPs are intentionally bracketed per responsible disclosure conventions. Do not attempt to access any listed indicators.