It Landed in My Primary Inbox
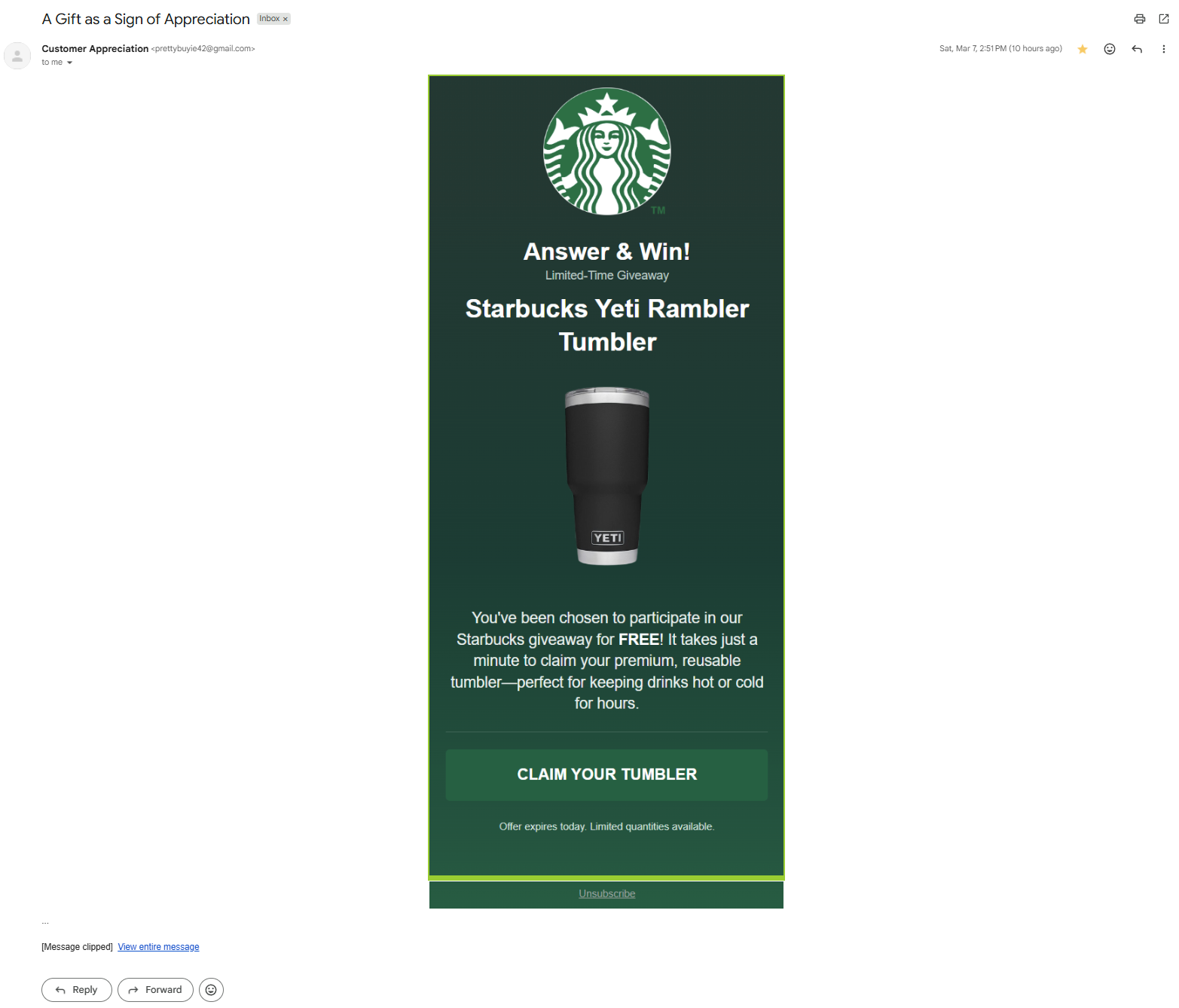
On March 7, 2026, I received a phishing email that most people would have clicked on without a second thought. Not because the lure was particularly sophisticated — it was a generic Starbucks Yeti Rambler Tumbler giveaway, the kind of brand impersonation scam that's been circulating for over a year. What made it notable was where it landed: directly in my Gmail primary inbox. Not spam. Not promotions. Primary.
For someone who receives a steady stream of phishing attempts, that's unusual. Gmail's classifiers are generally effective at routing unsolicited marketing and obvious phishing into secondary tabs or spam. The fact that this particular email bypassed all of those layers warranted investigation. What I found was a well-engineered phishing kit employing five distinct anti-spam evasion techniques working in concert, routing victims through a five-hop redirect chain across three cloud providers, and terminating at a fake antivirus scareware page designed to monetize fear through affiliate fraud commissions.
This writeup documents the full investigation: header forensics, infrastructure mapping, redirect chain deobfuscation, phishing kit fingerprinting, and correlation with known campaign families.
Pulling the Headers Apart
The email arrived from
Customer Appreciation <prettybuyie42@gmail.com> — a
throwaway Gmail account with no connection to any legitimate brand. But
the X-Google-Original-From header revealed the true origin:
1lAZtxmvQuFytG.CasVvkmNdeDhZ@visualstudio.com, a randomized
string abusing a Microsoft domain. The email was relayed through
mail.examples1.com at IP
147.185.243.153 before being injected into Gmail's SMTP
infrastructure via authenticated ESMTPSA.
Here's where it gets interesting. SPF, DKIM, and DMARC all passed — but
they validated against gmail.com, the envelope sender
domain, not against Starbucks or any brand the email claims to
represent. The attacker authenticated through Gmail's own submission
infrastructure, which means Google's trust chain effectively vouched for
the message.
The headers were also a Frankenstein of conflicting email service provider markers. X-headers from Sailthru, Salesforce Marketing Cloud, SendGrid, AWeber, and Klaviyo all appeared simultaneously. No legitimate sender routes through five ESPs at once. This is header stuffing — injecting trusted marketing platform identifiers to confuse reputation classifiers.
Other notable anomalies: the MIME type was declared as
multipart/report (a delivery status notification type)
instead of multipart/alternative; the
In-Reply-To and References headers referenced
message IDs at both visualstudio.com and
gmail.com, making it look like a reply in an existing
thread; and the header rcpt_domain: nike.com suggested the
template was recycled from a campaign targeting Nike customers.
One more detail that matters for clustering: the header
Content-Transfer-Enfcoding — a misspelling of "Encoding" —
appears in the DKIM signed headers. That typo is baked into the phishing
kit and can be searched across email threat intelligence platforms to
find other messages generated by the same tool.
Why It Beat Gmail — Five Evasion Layers
The primary inbox placement wasn't luck. It was the result of five distinct anti-spam evasion techniques stacked together, each reinforcing the others to create a compounding trust signal.
The email was injected through smtp.gmail.com using
ESMTPSA, causing SPF, DKIM, and DMARC to validate against Gmail's
own domain. Gmail inherently trusts mail that passes its own
authentication stack, even when the true origin is an external VPS.
The In-Reply-To and References headers
reference existing message IDs, making Gmail treat the email as a
reply within an existing conversation rather than a cold inbound
message.
The HTML body contains the entirety of an MS Research Australia newsletter (June 2017, Issue 47) embedded in hidden table rows. This floods Gmail's content classifier with tokens associated with educational, nonprofit, and health content, diluting the scam-associated tokens below the detection threshold.
Declaring Content-Type: multipart/report instead of
multipart/alternative causes the email to be evaluated
under heuristics designed for delivery status notifications —
system-generated messages that are almost never spam.
X-headers from five different email service providers (Sailthru, Salesforce Marketing Cloud, SendGrid, AWeber, Klaviyo) make the email's fingerprint resemble legitimate enterprise marketing infrastructure.
No single technique would likely have been sufficient. But the layered combination creates a situation where authentication validates the sender, threading establishes conversational context, Bayesian poisoning neutralizes content analysis, MIME abuse triggers relaxed rules, and ESP headers provide infrastructure legitimacy. It's a multiplicative effect.
Mapping the Sending Infrastructure
The originating IP 147.185.243.153 belongs to Kamatera (ASN
396948 / CLOUDWEBMANAGE-SC), a cloud VPS provider based in New York
operating datacenter infrastructure in San Jose, California. Scamalytics
rates Kamatera at 50/100 fraud risk, with approximately 50% of observed
web traffic flagged as potentially fraudulent.
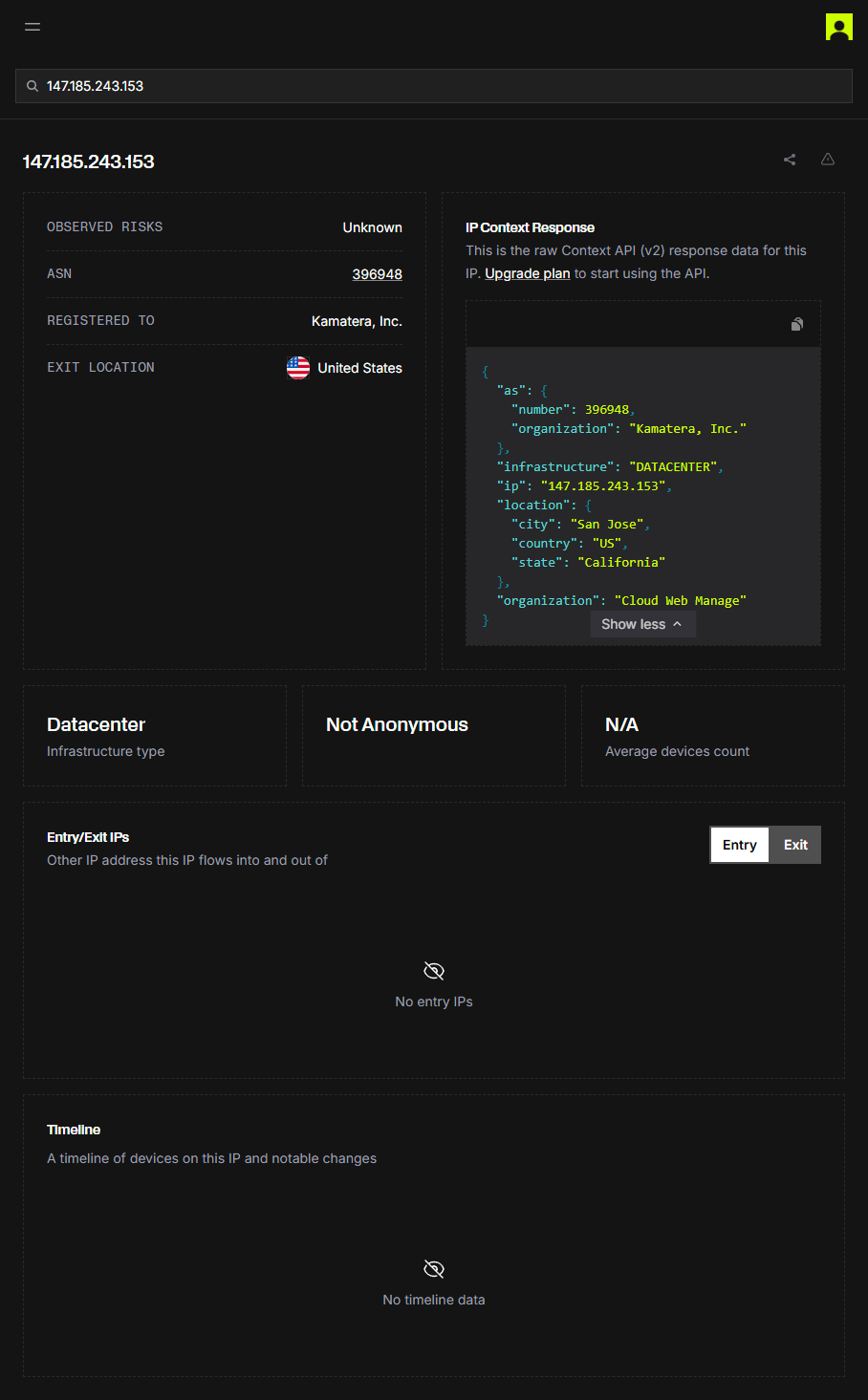
Passive DNS via Silent Push revealed four domains historically resolved
to this IP: okarun.site and
mail.okarun.site (active January 2026), plus
savbossmedia.xyz and
mail.savbossmedia.xyz (active November 2025). The
mail. subdomain pattern on both confirms this IP serves as
a dedicated mail-sending node for phishing campaigns.
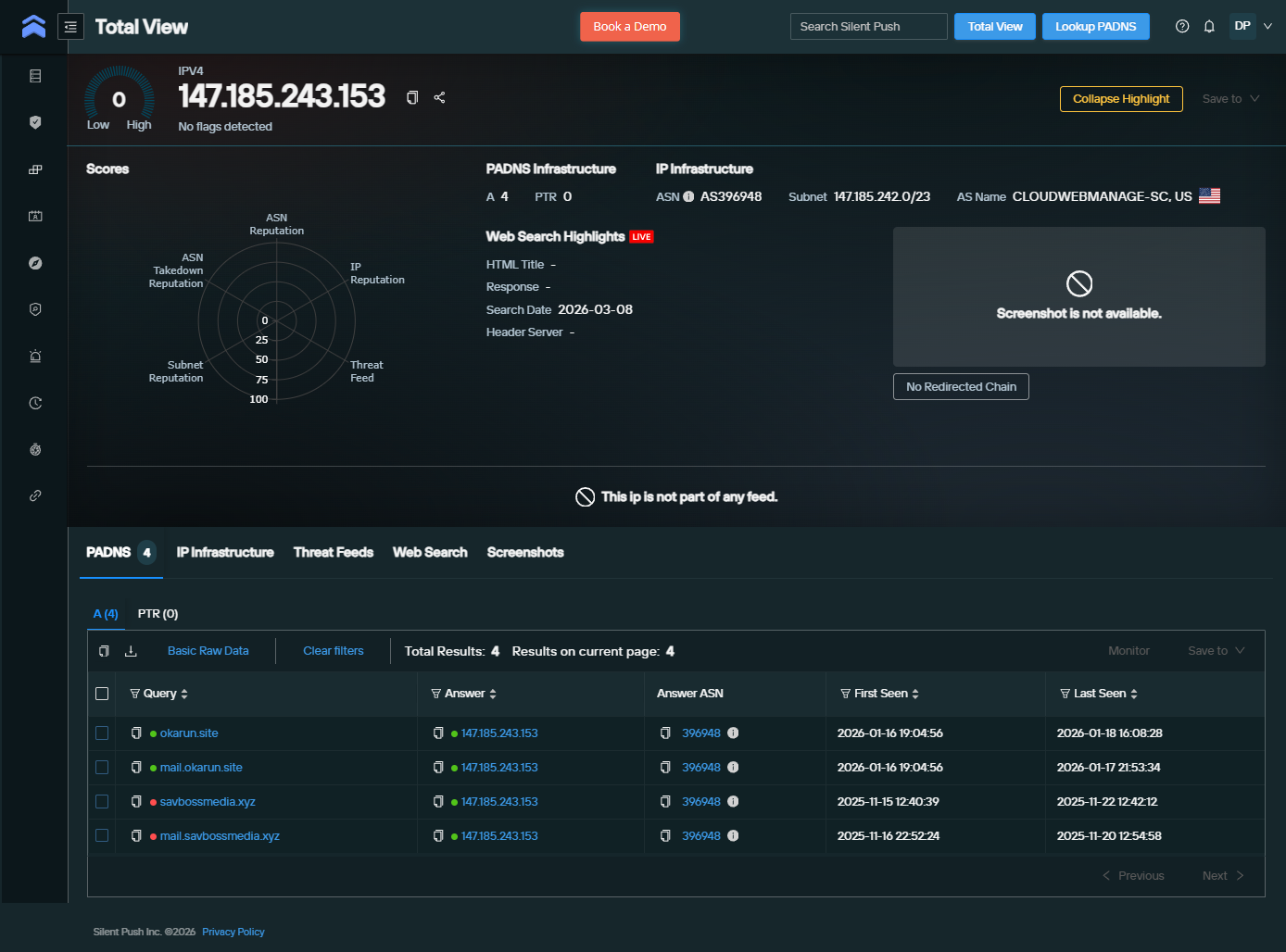
Certificate transparency logs (crt.sh) revealed that
okarun.site has hundreds of Let's Encrypt certificates with
new issuances every few days — a hallmark of automated, industrialized
infrastructure. This is not a one-off campaign; this is an operation
running at scale.
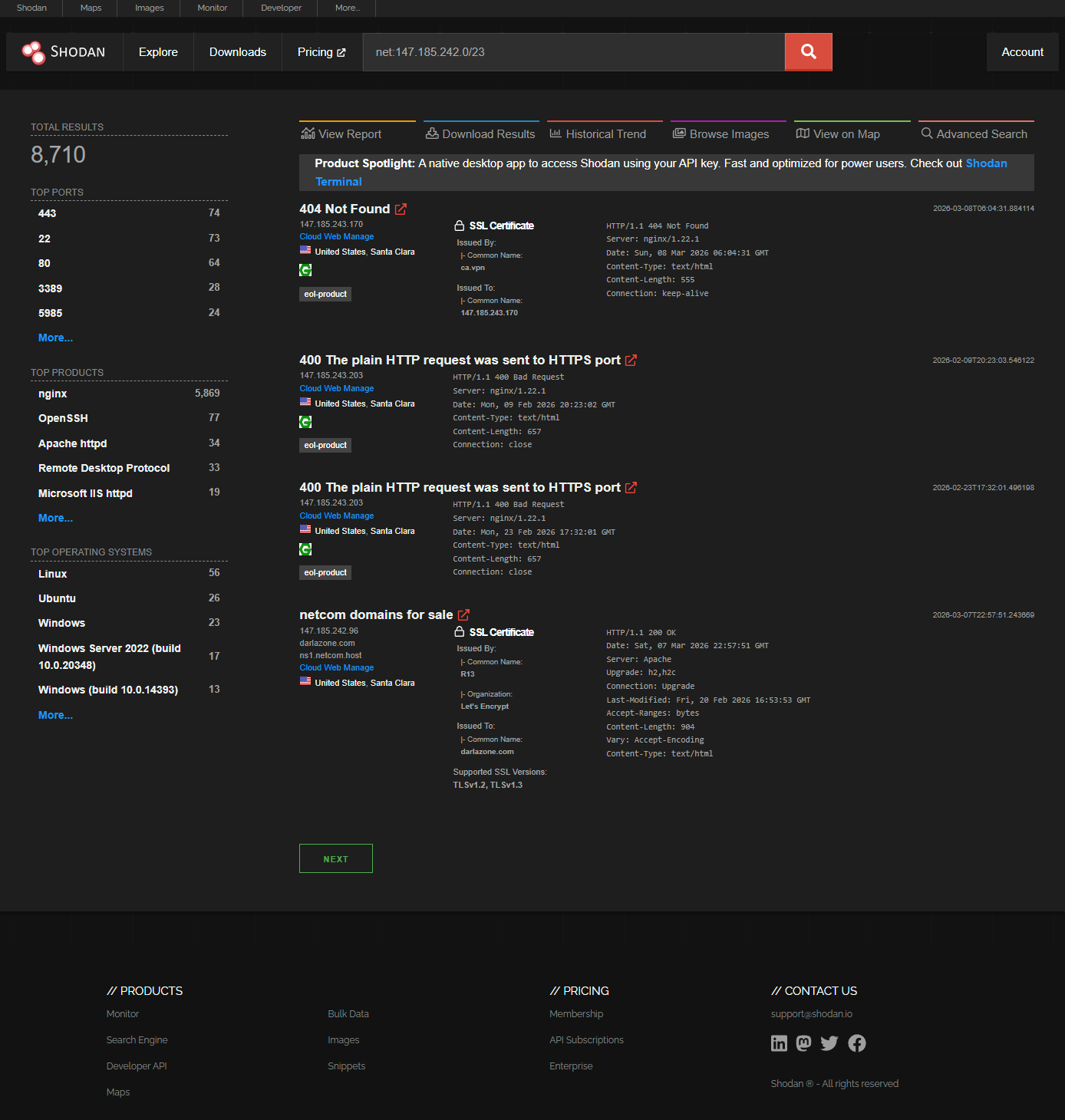
Shodan scanning of the /23 subnet returned 8,699 results. Two adjacent
hosts stood out: 147.185.242.98 runs
smtp.hufford.me — another mail server in the same block.
147.185.242.121 runs FlexBlaster Bot on
mail.dmpstuf.com — a mass-mailing tool commonly associated
with spam and phishing operations.
Following the Redirect Chain
The email's CTA linked to a DigitalOcean Spaces bucket with a
keyboard-mash name:
kdfbglsdjfngsldjbngsljbnlgjsg.nyc3.digitaloceanspaces.com/1.html. The URL included a hash fragment carrying affiliate tracking sub-IDs.
I submitted the URL to URLScan.io and examined the DOM capture. The page was only 603 bytes — a first-hop JavaScript redirector that extracts the hash fragment, splits it, and reassembles the values into affiliate tracking parameters for the next hop.
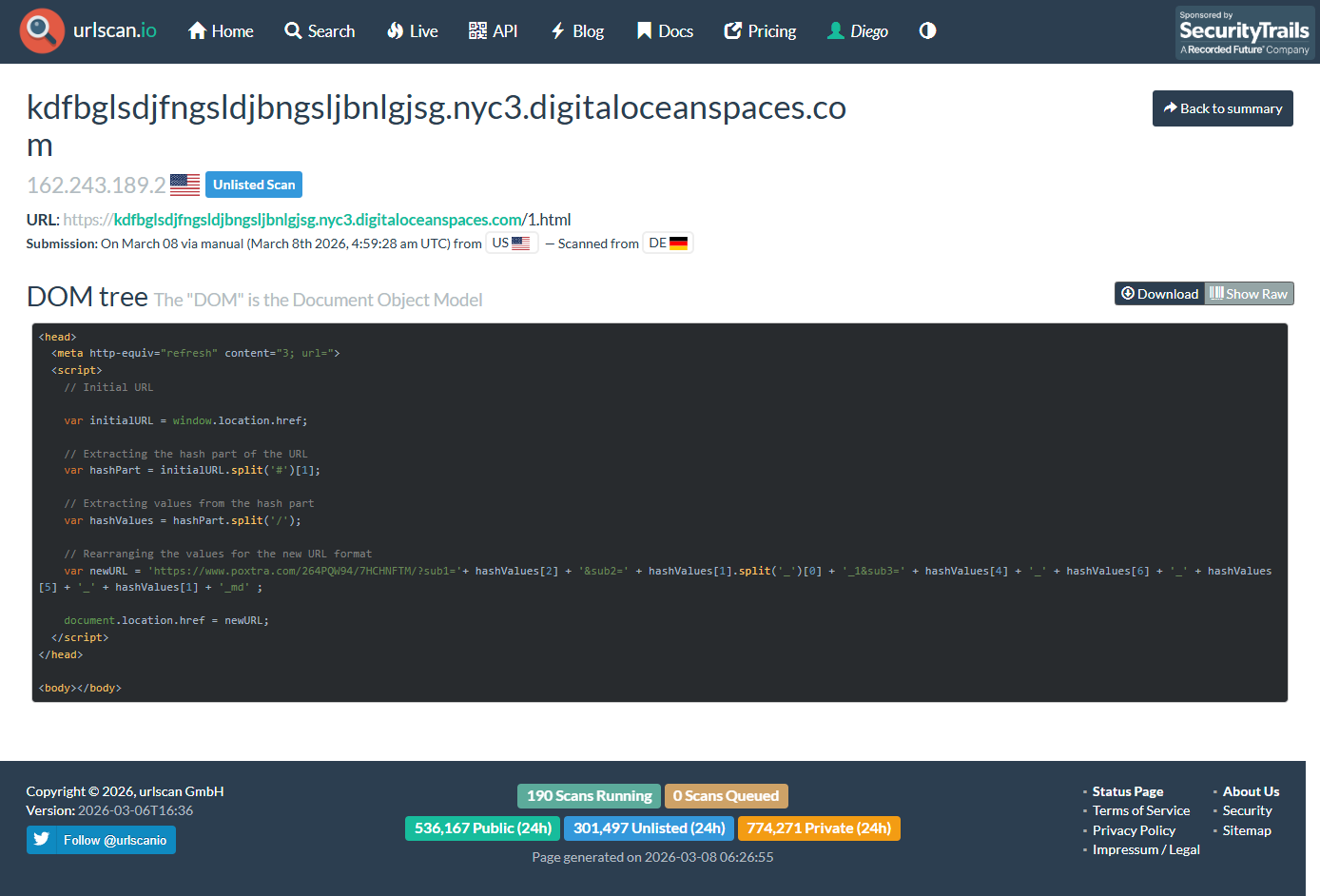
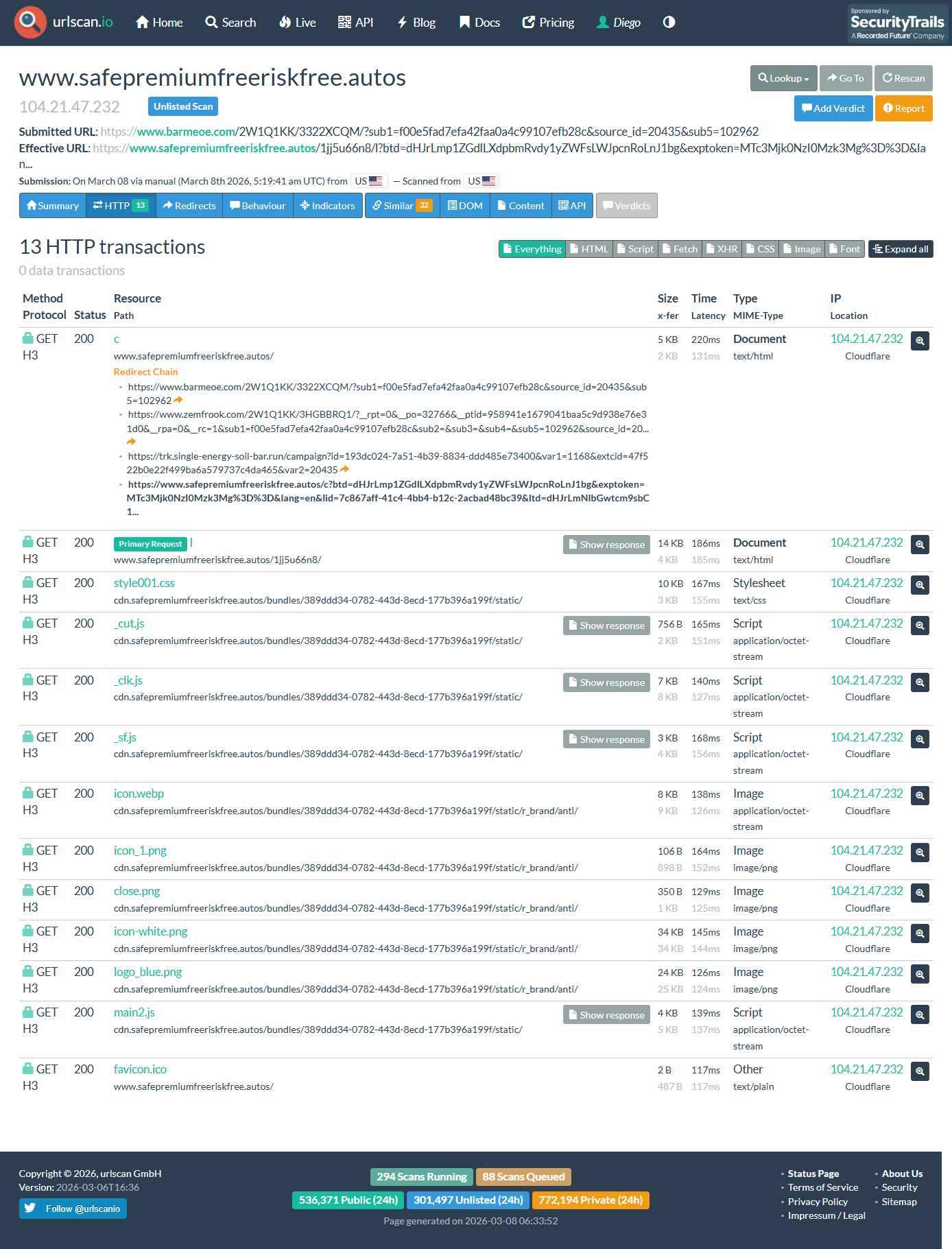
The complete five-hop kill chain:
prettybuyie42@gmail.com via
147.185.243.153. Lure: Starbucks Yeti Rambler
giveaway. Link target: DO Spaces bucket with hash fragment.
/1.html. Function: Extract
hash fragment, reassemble into affiliate tracking URL. Size: 603
bytes, zero visible content.
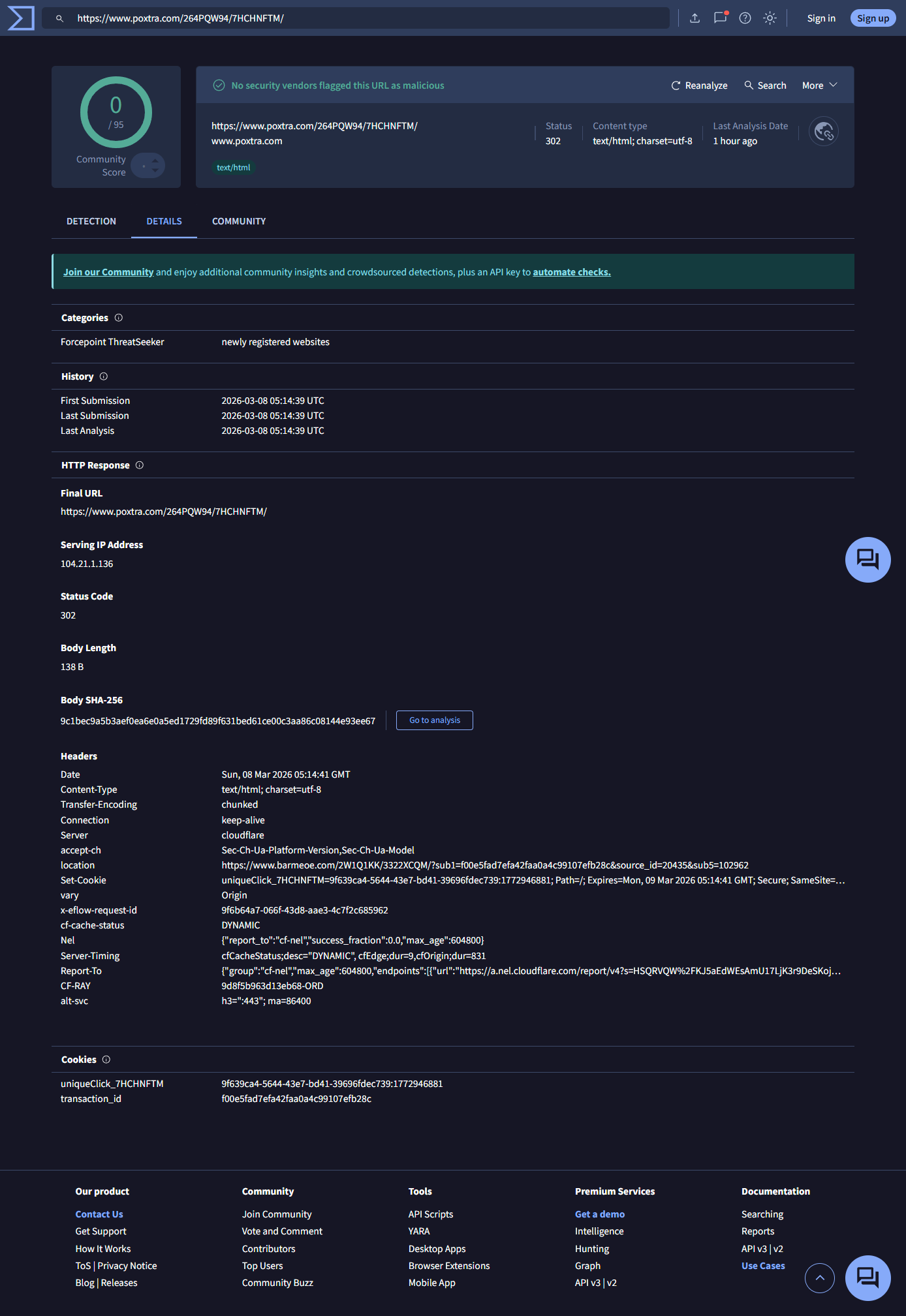
poxtra.com/264PQW94/7HCHNFTM/. Response: HTTP
302 redirect. Cookie: uniqueClick_7HCHNFTM.
Tracking: source_id=20435,
sub5=102962.
barmeoe.com/2W1Q1KK/3322XCQM/. Response: HTTP
302 redirect. Cookie: uniqueClick_3322XCQM.
zemfrook.com →
trk.single-energy-soil-bar.run. Final:
safepremiumfreeriskfree.autos. Content: Fake
antivirus scareware — "WARNING: Antivirus Protection EXPIRED!"
All three broker domains (poxtra.com,
barmeoe.com, zemfrook.com) follow the same
registration pattern: Namecheap registrar, Withheld for Privacy ehf,
Cloudflare fronting, sequential creation dates (January 24 and February
3, 2026).
The End of the Chain — Scareware for Profit
The final landing page at
safepremiumfreeriskfree.autos displays a fake antivirus
expiration warning: "WARNING: Antivirus Protection EXPIRED!" with
urgency language and a "RE-ACTIVATE" button. The page title is "Security
Center."
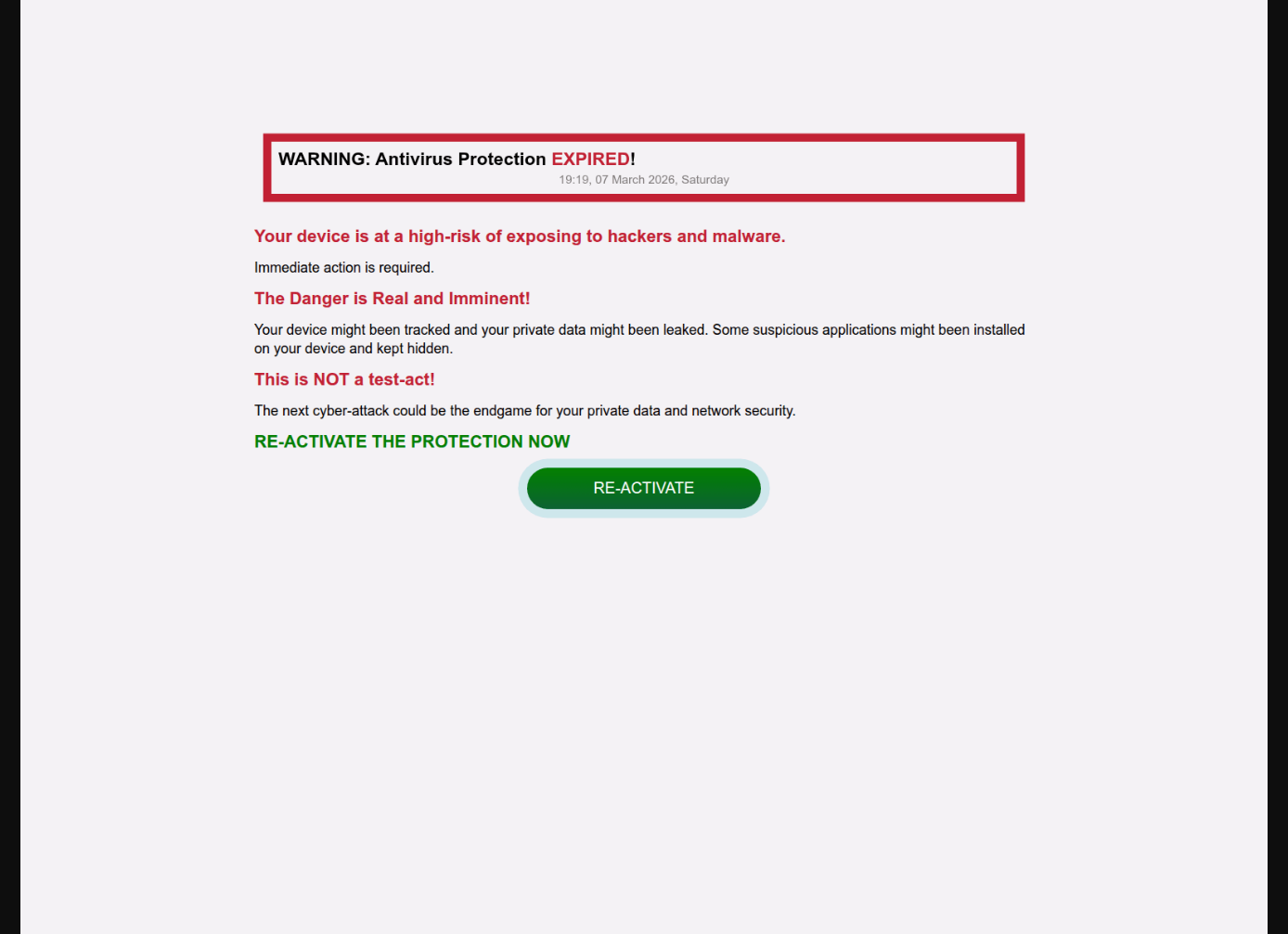
The trk.single-energy-soil-bar.run tracking domain with
source_id and campaign parameters confirms this is an
affiliate fraud operation. The actor (source_id=20435)
earns a CPA commission for every victim who clicks through. The
"RE-ACTIVATE" button likely either pushes a legitimate AV affiliate
purchase or downloads a PUA/malware payload.
The operation has diversified its monetization. Earlier public reporting (Botcrawl, November 2025) documented this campaign family terminating at credit card harvesting checkout pages. This March 2026 variant pivots to scareware affiliate fraud instead, showing the operator adapting while keeping infrastructure patterns identical.
32 Pages, Same Kit
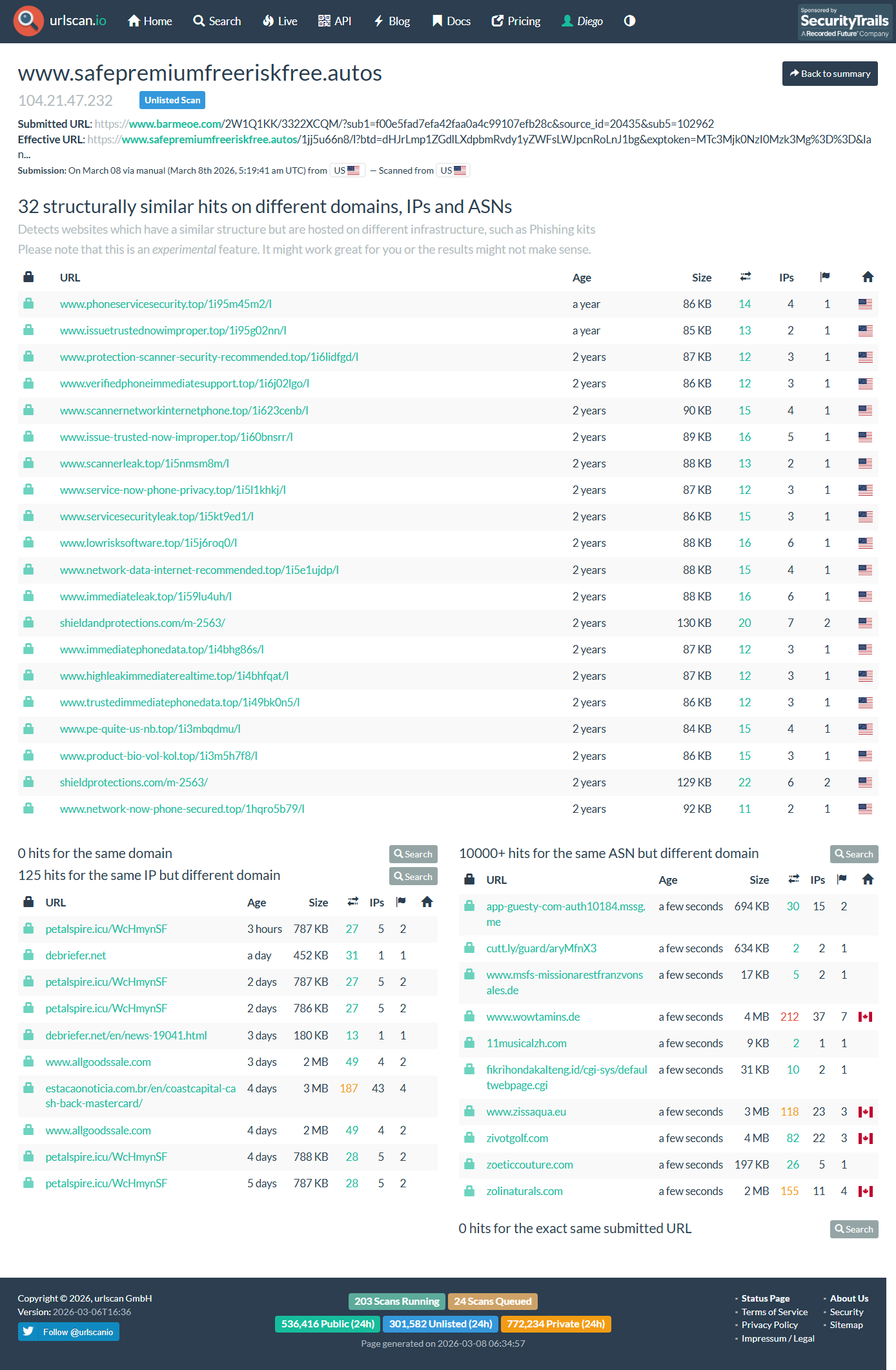
URLScan's structural similarity engine identified 32 pages with matching
structure across different domains, IPs, and ASNs. The domains follow
descriptive naming patterns: phoneservicesecurity.top,
protection-scanner-security-recommended.top,
verifiedphoneimmediatesupport.top,
scannerleak.top, and many others. These span approximately
two years.
A Known Campaign Family
Open-source research confirms this is part of a well-documented campaign:
Botcrawl (November 2025) published a teardown of the same Starbucks Yeti Rambler lure with identical operational patterns. Botcrawl (December 2025) documented a Starbucks Bearista Cup variant. Bitdefender Antispam Labs confirmed global scope, with the US as the primary target at 35%. Gen Digital's Q2/2024 Threat Report documented the broader category — fake AV scams exploiting affiliate programs for commissions.
The complete five-hop redirect chain, the pivot to scareware
monetization, the five-layer anti-spam evasion analysis, Kamatera
infrastructure mapping, FlexBlaster Bot co-tenancy, the
Content-Transfer-Enfcoding kit fingerprint, and the
Bayesian poisoning technique using a specific 2017 medical newsletter.
Indicators of Compromise
| Sender | prettybuyie42@gmail.com |
| Original From | 1lAZtxmvQuFytG.CasVvkmNdeDhZ@visualstudio.com |
| Subject | A Gift as a Sign of Appreciation |
| Campaign ID | 511517 |
| X-rpcampaign | stcsp86697076 |
| Kit Fingerprint | Content-Transfer-Enfcoding (misspelled header) |
| IP | 147.185.243.153 (ASN 396948 / Kamatera) |
| Domain | okarun.site / mail.okarun.site |
| Domain | savbossmedia.xyz / mail.savbossmedia.xyz |
| Adjacent | 147.185.242.98 (smtp.hufford.me) |
| Adjacent | 147.185.242.121 (FlexBlaster Bot / mail.dmpstuf.com) |
| DO Spaces | kdfbglsdjfngsldjbngsljbnlgjsg.nyc3.digitaloceanspaces.com |
| Broker | poxtra.com (Namecheap, 2026-01-24) |
| Broker | barmeoe.com (Namecheap, 2026-02-03) |
| Broker | zemfrook.com |
| Tracker | trk.single-energy-soil-bar.run |
| Landing | safepremiumfreeriskfree.autos (NameSilo, 2025-10-04) |
| Source ID | 20435 |
| Campaign ID | 193dc024-7a51-4b39-8834-ddd485e73400 |
| Sub5 | 102962 |
Takeaways
Layered evasion works. The combination of authenticated Gmail relay, conversation threading injection, Bayesian poisoning, MIME type abuse, and multi-ESP header stuffing represents a sophisticated approach to bypassing modern email classifiers. Together they compound into a trust signal that even Gmail accepted.
The operation is persistent and adaptive. The same campaign family has been running for over a year, rotating brand lures, infrastructure, and monetization endpoints. The 32 structurally similar URLScan results confirm industrial scale.
Email authentication doesn't mean legitimacy. SPF, DKIM, and DMARC all passed. Those protocols verify the sender identity, not content legitimacy.
Affiliate fraud enables the ecosystem. The five-hop
chain with source_id and sub parameters
confirms a multi-tier affiliate model that remains financially viable as
long as CPA networks don't police traffic sources.
CrimsonVector — Investigative research by Diego Parra mapping, and security research.